Feeling watched online? Discover what data mining is, what the threats are, and learn how to protect yourself with the best free VPN.
Have you ever searched for a product online, only to see ads for it follow you across different websites? Or perhaps you noticed that your social media feed is filled with content eerily aligned with your recent interests? These is no such coincidence. You see those because companies will use data mining to analyze your behavior to refine their market and push products.
Although it might feel nice and personal at first, it also gives others a clear picture of your own life, which means something could put your privacy at risk. That’s why we are here to show you how to protect yourself from data mining.

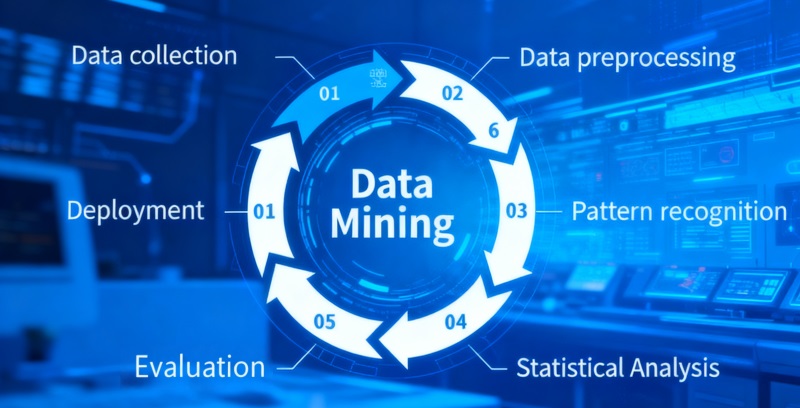
In simple terms, data mining is the process of discovering patterns and useful information from large sets of data. Some companies will use it to see what’s trending, understand what customers want, and plan their next move. But how does it actually work? The data mining process typically follows these steps:
Data Collection: Vast amounts of raw data are gathered from your online activities—what you click, what you buy, where you are, and what you search for.
Data Processing: The collected data is cleaned and organized into a structured format for analysis.
Pattern Analysis: Once the data is cleaned and organized, computers look for regular patterns or links between different pieces of information.
Application Output: Companies then use these discoveries to influence what you see online. The results are all around you: the perfectly timed ad, the video that auto-plays next, or the "customers also bought" section on a shopping site.
Understanding how data mining works naturally leads to concerns about how it impacts our digital lives, and of course, how to protect yourself from data mining. Here are the primary risks you should be aware of:
Information and Data Breaches: Centralized databases filled with mined personal information are prime targets for hackers. A single security failure can lead to your sensitive data being exposed or sold on the dark web.
Excessive Behavioral Monitoring: Your every click, scroll, and pause can be tracked, recorded, and analyzed.
Data Trading and Misuse: Your personal information is a valuable commodity. Companies often package it up and sell it to middlemen, who then turn around and sell it to others. These buyers might use it to target you with spammy ads, or even worse, try to trick you into taking out a high-interest loan.
Identity Theft: With enough mined data, such as your birthdate, address, and social security number, malicious actors can impersonate you to commit fraud or open accounts in your name.
Manipulation and Discrimination: In the end, you might be reduced to a simplified "label." This label can be used to manipulate what you buy. It can also be used to discriminate against you, leading to higher insurance premiums, rejected job applications, or unfair loan conditions, all decided automatically by a system that thinks it knows you.
Also Read: Best Free TikTok VPN to Unblock TikTok with VPN for PC & Mobile >>
So, what can you do after you know the threats of data mining? Don't worry! Here are at least eight effective solutions, covering app usage habits, protective tools, and awareness enhancement.

Control App Permissions: Regularly review and restrict the permissions you grant to mobile apps and browser extensions. Deny access to your contacts, location, and microphone if it's not essential for the app's core function.
Be Careful in Providing Personal Information: Think twice before filling out online forms or participating in surveys. Only provide the minimum amount of information necessary.
Use a VPN: A free VPN is one of the most powerful tools for how to prevent data mining. Think of it as putting your internet connection into stealth mode. For anyone trying to monitor you—like data miners and advertisers—it's like you've suddenly vanished. This is a core part of using a VPN data mining protection strategy.
Use Browser Extensions: Install privacy-focused extensions like ad-blockers, anti-tracking tools, and script blockers. A good data mining extension can stop websites from tracking and collecting your data.
Use a Privacy-Focused Browser and Search Engine: Switch to browsers like Brave or Firefox with strict privacy settings, and use search engines like DuckDuckGo that do not track your searches.
Regularly Clear Cookies and Cache: Cookies are often used to track your activity across the web. Regularly clearing them disrupts the data collection process.
Read Privacy Policies: While tedious, understanding how a company collects and uses your data can help you make informed decisions about which services to use.
Keep Your Software Updated: Regular updates often include critical security patches that fix vulnerabilities which could be exploited to steal your data.
As highlighted, using a reliable VPN is a cornerstone of protecting your privacy. It is to be mentioned that iTop VPN is an excellent choice. Designed to block IP tracking and hacking attempts, it also shields your privacy from VPN data mining. For instance, when you're using public Wi-Fi, a VPN encrypts your connection to prevent eavesdropping, and it also hides your real location when browsing, stopping websites from building a geographical profile of you.
Here’s how iTop VPN stands out:
AES-256 Encryption: This military-grade encryption scrambles your internet data, making it unreadable to anyone who might intercept it, including your Internet Service Provider (ISP) and data miners.
No-Log Policy: iTop VPN is committed to your privacy. They follow a strict no-log policy, meaning they do not track, store, or share any of your online activity data.
Global Servers to Hide IP: By connecting to one of their global VPN servers, you can mask your real IP address with one from a different location.
Double VPN: By sending your data through two separate servers, this feature encrypts your connection twice—making it much harder for anyone to trace or intercept your activity.
Also Read: 8 Best Free IP Stresser & IP Booter 2025 >>
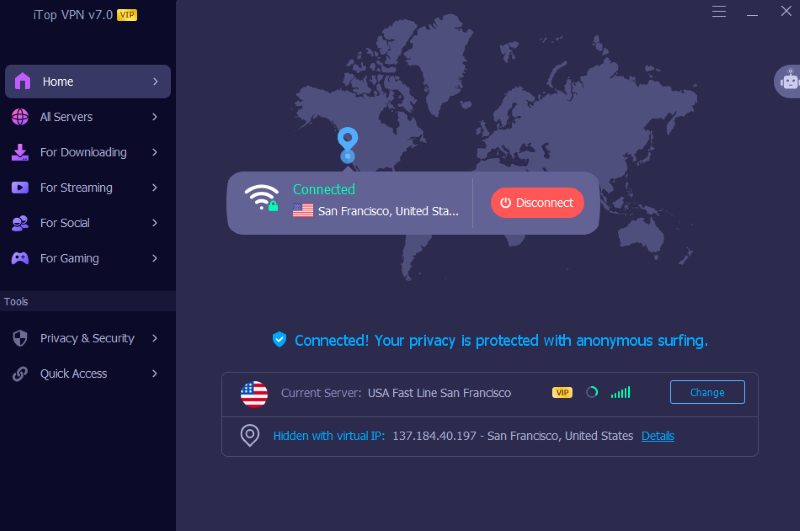
Protecting yourself with iTop VPN is a straightforward, three-step process:
Step 1: Download the iTop VPN app onto your device (PC, Android, or iOS) by clicking the button below.
Step 2: Install and launch the application. You can create an account or start with the free service immediately.
Step 3: Navigate to the All Servers tab, then select a server location from the list and click the "Connect" button.

Step 4: Within seconds, your connection will be secure and private. Now you can freely browse content on the internet without worrying about the risks of data mining.
For specific needs like accessing a dedicated IP VPN, you can also explore their premium options.
It's important to distinguish between data mining and a data breach, as they are often confused.
Data Mining: This is a structured analytical process used to uncover valuable insights and patterns in data, often for business strategy and optimization
Data Breach: This is a security incident. Its core characteristic is the unauthorized access, disclosure, or theft of confidential data by an external or internal threat. It is an accidental or malicious event and is almost always illegal.
The key difference lies in intent and legality: data mining is an analytical tool, while a data breach is a security failure. However, they are connected. Or let’s say, the more data collected, the more privacy leaking by data mining process. Therefore, a company engaged in heavy data mining increases the potential impact of a future data breach.
Conclusion
Today, data mining has become widespread, bringing genuine concerns over personal privacy. Not only behavioral monitoring, but data breaches, the threats are real and everywhere.
However, as we've outlined, you are not powerless. That’s why you need a robust VPN which can significantly reduce your digital footprint. For a comprehensive and easy-to-use solution, iTop VPN is highly recommended. Start with iTop VPN 7 day trial from now!
10+ free servers in US, UK...
3200+ extensive servers
Dedicated IP addresses
Ad blocker and Proxy service
For Windows 11/10/8/7